The Ultimate Guide to Access Control
This four part series guide provides a comprehensive introduction of how access control is achieved. The first post by introducing access control key terminology and then dives into the different types of systems and credentials, as well as how those can be remotely controlled through Seam’s products. Subsequent posts cover Smart Locks, Access Control Systems and Intercoms.
Access control refers to the practice of limiting access to a physical space or digital resource, such as a digital file or building or a room, to authorized users only. Access control is achieved through various means, from traditional lock and key systems to modern smart locks and multi-door access systems.
Part 1: Introduction to Access Control Terminology & Concepts
Access control is the practice of regulating who has access to a physical or digital space, asset, or resource. In other words, access control is all about “who does what and to what”. It’s based on the access control policy and controls who gets in and out of the system (or physical space), who gets what resources (in case of the digital systems) and when that happens. In this post, we’ll cover main terminology and main types of access systems and credentials.
Access Control Atomic Primitives
There are four core elements to access control:
- Subjects: actors/users or groups of users that need access to resources (objects), eg., maintenance staff, Airbnb renter
- Objects: resources to access, eg., digital files, rooms
- Operations: what operations subjects can perform on objects, eg., download, open/unlock.
- A reference monitor: stores policies and rules and who is allowed to do what and when.
Therefore atomic primitives play a central role in defining the types of access control.
Types of Access Control: DAC, MAC, and RBAC
The relationship between subjects, objects, and operations are generally organized into three main types of access control:
- Discretionary Access Control (DAC): This is the most basic type of access control, in which the owner of a resource has complete control over who is allowed to access it. The owner can grant or revoke access as they see fit, and there are no restrictions on who can access the resource.
- Mandatory Access Control (MAC): This type of access control is used in high-security environments, such as government agencies or military installations. In a MAC system, access is determined by a set of predefined rules, rather than by individual users. For example, a user's security clearance level may determine what resources they are allowed to access.
- Role-Based Access Control (RBAC): This type of access control is based on the idea of assigning users to different roles, each of which has a specific set of permissions. For example, a manager might have permission to access certain files or rooms that a regular employee does not. RBAC is commonly used in organizations to ensure that employees only have access to the resources they need to do their jobs.
It’s important to understand the type of access control. Next, let’s look at types of credentials being used.
Credentials & Verification
Before access can be granted, a person must first present a credential. There are many types of credentials and verification processes:
- Key-based access: This is the most common form of access control, where a lock and key are used to allow authorized individuals to access a particular area.
- Badge and fob-based access: This involves the use of badges, fobs, or ID cards that are issued to authorized individuals. The badge contains a magnetic stripe or RFID chip that is scanned at the entry point.
- Mobile-based access: in this instance, a credential is loaded onto a user’s mobile device. This device then presents the credential to an access point, usually via Bluetooth or NFC, in order to obtain access for the user.
- Biometric-based access: This type of access control uses a person's unique biological traits such as fingerprint, facial recognition, iris scan or voice recognition to allow entry.
- PIN-based access: This involves the use of a personal identification number (PIN) that is entered into a keypad or other device to allow access.
- Physical token-based access: This type of access control charges money with coins or tokens for access, e.g., public restrooms, metro/subway.
- Human-verification-based access : This type of access control involves a human (either in person or remote) who manually checks the credentials of individuals seeking entry. Examples include security guards or residents of a building receiving using an intercom.
The aforementioned access types can be combined, for example visitor management or personnel accesses can use badges (cards).
As with many things in life,each credential type has their own pros and cons. Let’s discuss the main pros and cons of main credential types: keys vs. badges vs PIN codes.
Physical keys are economical but cumbersome to share with a visitor. They can also be lost or duplicated without permission, creating unauthorized access risk. The only remedy is often a rekeying operation of each compromised lock, which can be expensive.
Similarly, badges, IDs, and fobs also require a physical exchange to grant visitor access and can be lost or copied. However, a compromised badge or fob can generally be deactivated from a centralized system without requiring any rekeying operation.
Lastly, PIN codes and mobile-keys are by far the easiest to share since they can simply be emailed to a visitor. Like badges and fobs, they’re also easy to deactivate from a system. However, not every door access point will have a keypad to input a PIN code or have the ability to receive a mobile key presented over bluetooth or NFC. The latter feature is only supported by the more modern hardware systems and could require a system upgrade.
Therefore, when picking a credential type, an operator should evaluate how often credentials need to be shared, how costly a compromised credential might be to mitigate, and whether there is a budget for upgrading access points to more flexible credentials such as mobile keys.
We’ve covered the credential types. Now, let’s look at types of access systems.
Types of Access Systems
An access system receives a credential as input and outputs a decision to grant or not to grant access. At Seam, we usually classify access systems into 4 categories:
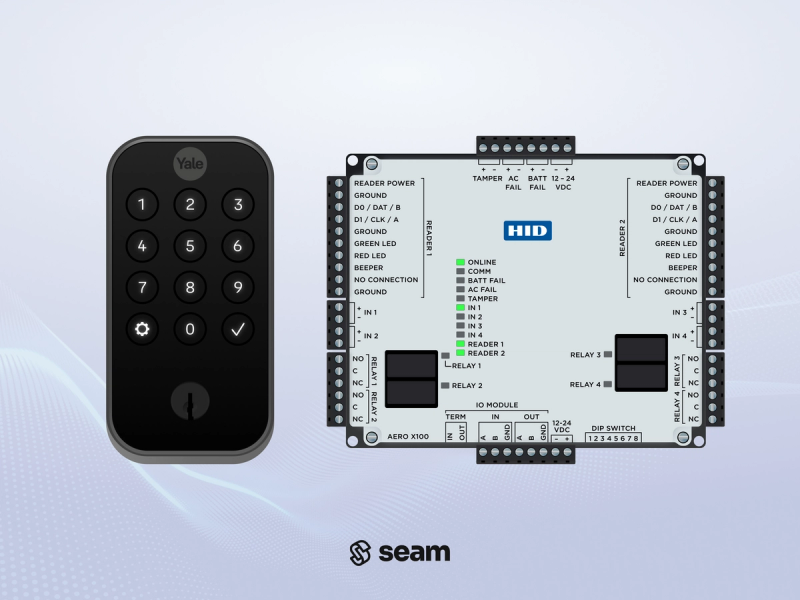
- Individual Smart locks – these control access to a single door. They usually accept a PIN code, a physical key, a fob, or a mobile key, and look up the credential in the device’s memory. If the credential is known and valid, the device grants access.
- Access Control Systems (“ACS”) – these are most common in larger buildings and can control hundreds of doors. A user will usually present a credential to a reader (e.g. a card reader). This credential information is then relayed to the ACS’s central controller which looks up the credentials in an internal database. If the credential is known, the central controller sends an unlock signal to the door situated next to the reader where the credential was presented.
- Intercoms – these are common outside of apartments and some office buildings. They allow a visitor to contact and communicate with a resident. The resident can then decide to grant access or not. The intercom is usually able to trigger an unlock on the adjacent door.
- Gates – they are usually found outside of parking structures or gated communities. A reader located next to the gate will receive credential input and make determination whether or not to open the gate. Note that some gates are connected to an ACS.
The four categories are not black and white. They are often combined and interloop, e.g., an apartment complex can have ACS, intercoms and gates. An individual single-family home can have gates and individual smart locks not connected to each other.
Conclusion
To sum up, access control comprises a set of primitives such as people and actions, and is governed by a set of access policies (e.g. RBAC). To gain access, a user must present credentials. Credentials have various pros and cons. Physical credentials are difficult to share, hard to track, and readily compromised. This can lead to expensive rekeying operations. Meanwhile, novel credential form-factors, such as mobile keys, are easy to share and track, but require newer access systems to be installed.
The rest of this guide will cover each access control type in-depth, starting with smart locks.